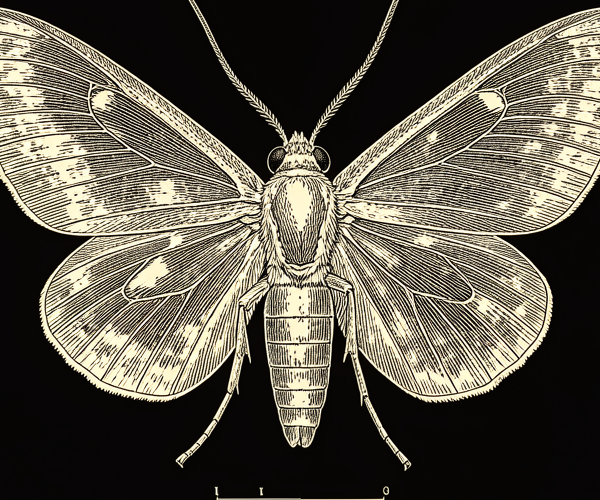
The first bug
Every unknown error starts as confusion. The machine stops working. Nobody knows why. What follows is the search. In 1947, the search was simple and the answer was physical. It wouldn't stay that way.
On September 9, 1947, operators of the Harvard Mark II found a moth stuck in Relay #70, Panel F. They taped it into the logbook with the annotation: "First actual case of bug being found."
The word "bug" for a technical glitch predates this by decades. Edison used it. So did engineers in the 1870s. What Hopper's team found wasn't the origin of the term. It was just the first time the metaphor got literal.
The Mark II was an electromechanical computer. Relays opened and closed thousands of times per second. A moth, doing moth things, flew into one and died. The relay stuck. The machine stopped making sense.
They found it. They fixed it. They moved on.
The moth is now in the Smithsonian, still taped to the logbook page. It's probably the most famous dead insect in history, and it earned that distinction by doing nothing more complicated than flying toward a light.
There's something satisfying about an error this clean. A physical object in a physical machine causing a physical failure. You open the panel, you see the moth, you remove the moth. Debugging at its most literal and its most optimistic: every error has a cause, every cause can be found, and the fix is obvious once you find it.
That optimism would not survive the century.
Smithsonian National Museum of American History — the original moth is in their collection, taped to a log book page from the Harvard Mark II.